Cybersecurity weather forecast – 3rd quarter 2021

There are very divergent trends to note in this first weather report of the year. Phishing is still the leading cause of security incidents, but the quarter saw vulnerabilities being actively exploited by hacker groups, as well as the emergence of malicious code.
General information
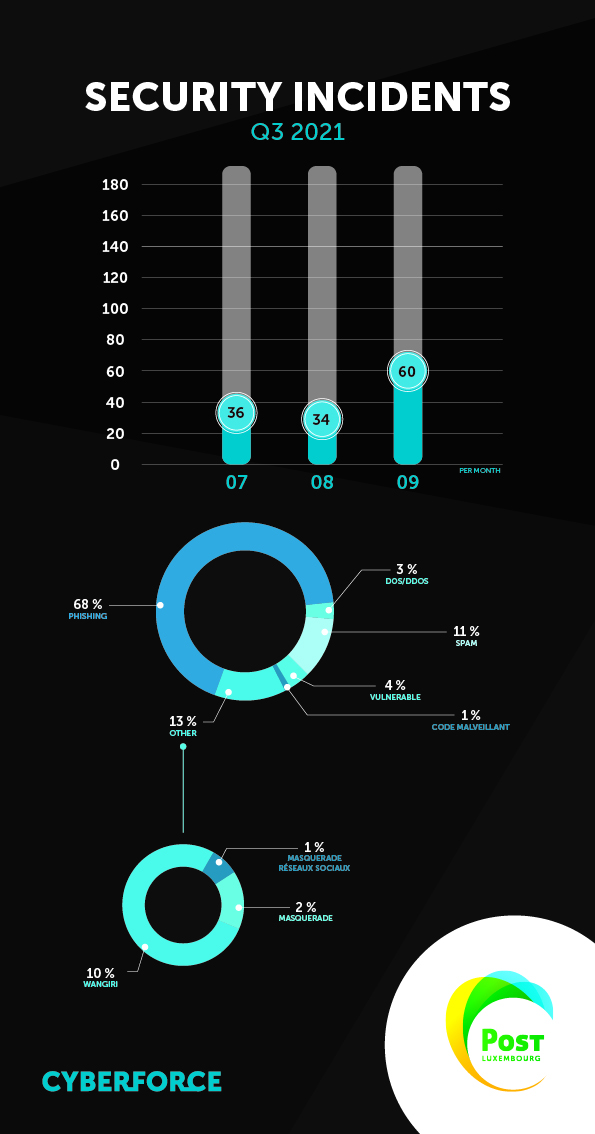
The figures for incidents recorded by the POST CyberForce CSIRT confirm the downward trend in incidents with an upturn in September. The July and August figures represent the lowest number of recorded incidents since the first cybersecurity weather forecast. The upturn in September corresponds to a significant increase in the number of phishing attacks during the month. Accounting for 68% of incidents over the period, phishing remains the most serious issue. On the malware side, the threat is changing.
Phishing
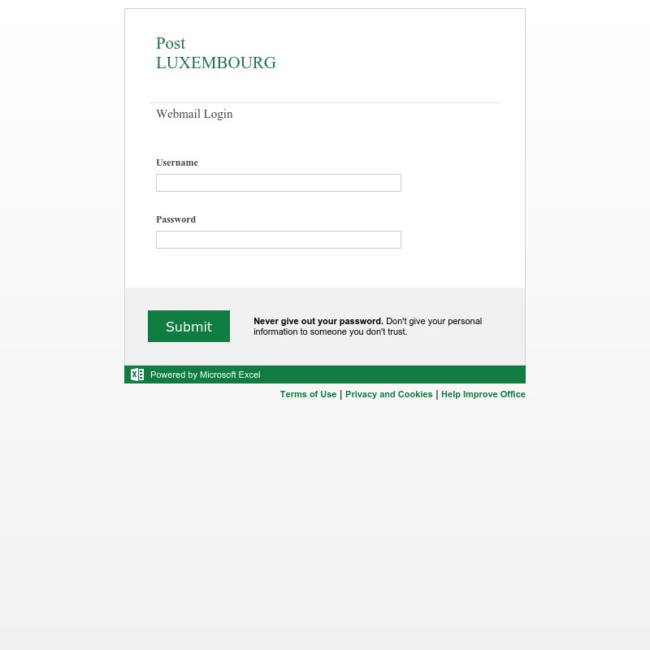
In this period, the bulk phishing techniques used mainly related to malicious actors’ aim of hacking into residential e-mail accounts ending in "@pt.lu". The level of care taken by malicious actors in such attacks varies greatly depending on the intended target: some attacks use kits that imitate web pages almost perfectly, while others reuse existing kits with nothing but a change of logo. In bulk phishing cases, we also see the online Microsoft Excel app being used.
We have also noticed two categories of spearphishing (i.e. targeted phishing) against companies:
- Outlook Web Access page spoofing
- Use of corporate Microsoft Azure pages
In Outlook Web Access spoofing, the malicious actor initially seeks to gain access to the webmail associated with a targeted account belonging to a company user.
In an attack via a Microsoft Azure page, the target is often one of the company’s user accounts, especially when the company has migrated part of its infrastructure to the Microsoft Azure cloud. In these specific circumstances, the malicious actor initially seeks to gain access to the company’s cloud environment. Measures can be taken to protect against this type of threat, such as two-factor authentication and restrictions specific to the company's tenant (profile).
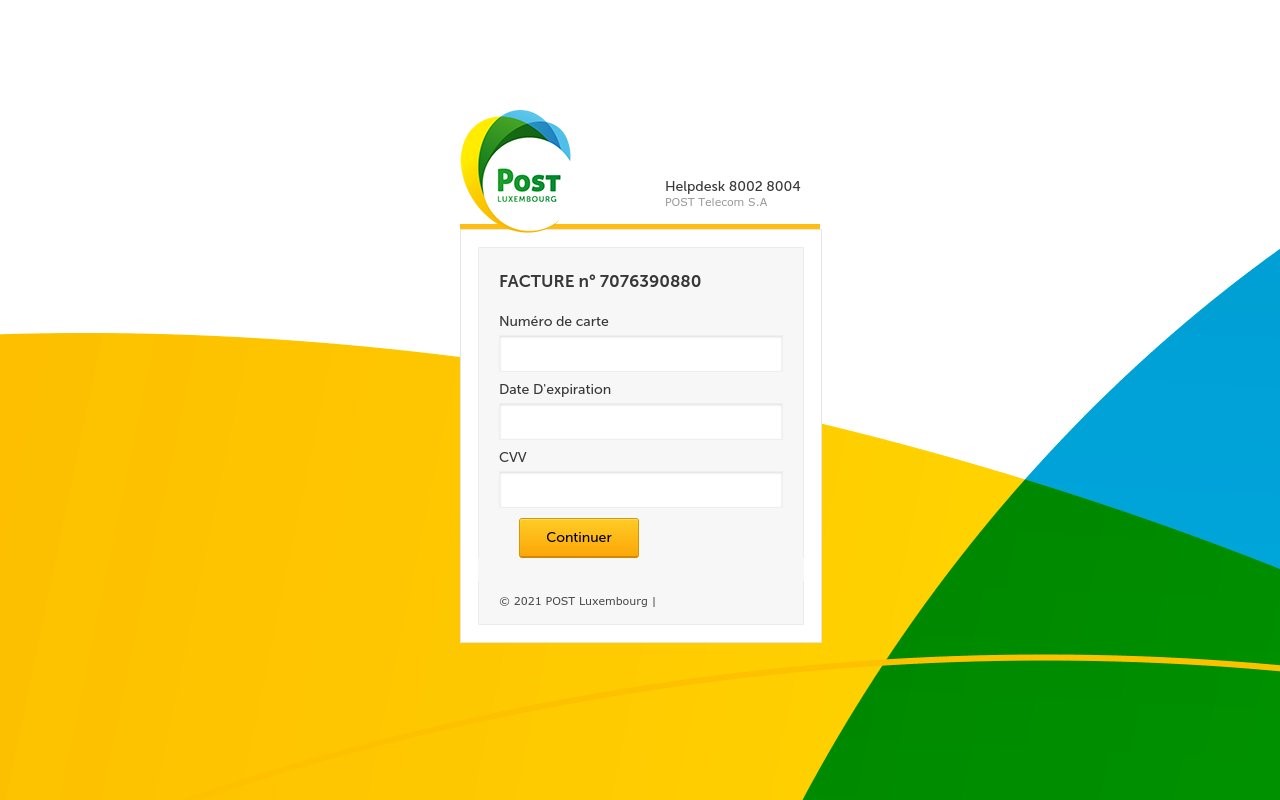
Here are some screenshots of phishing web pages captured during the period:
Outlook :
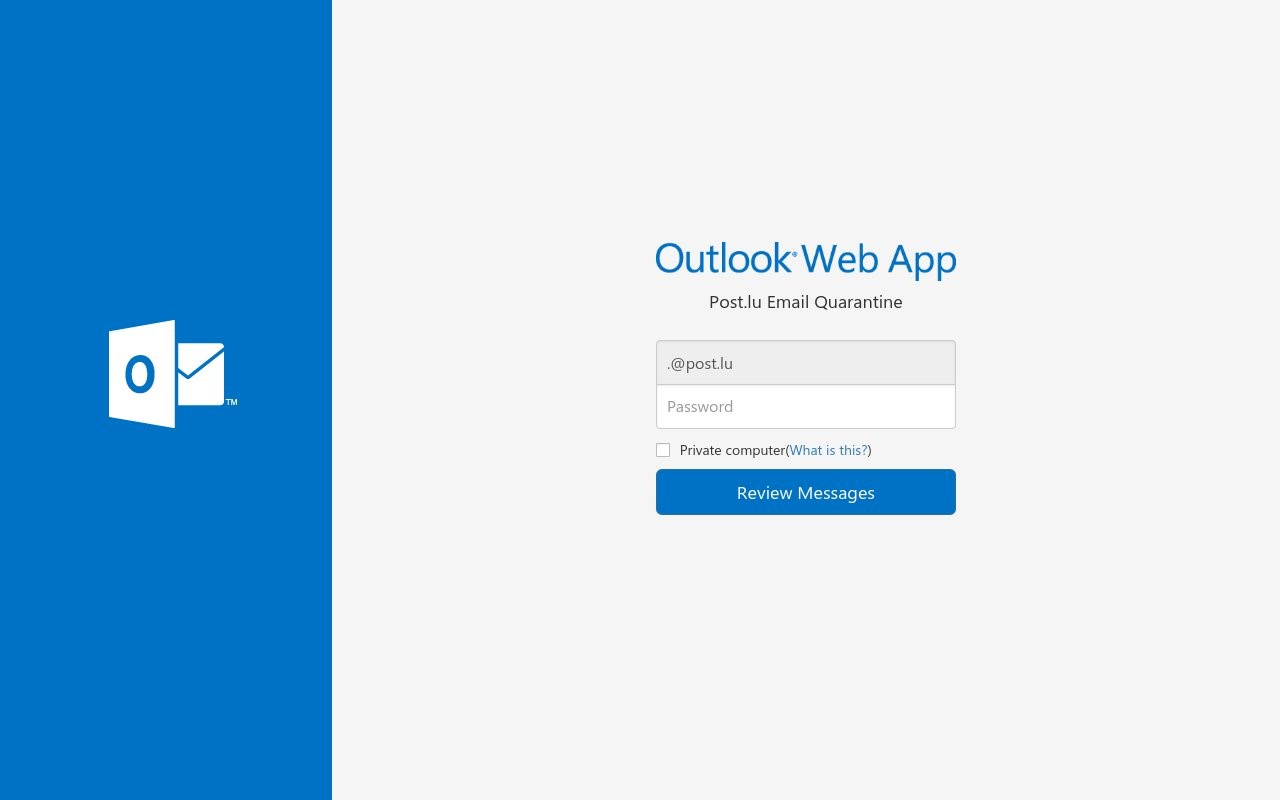
Designing web pages with care increases their credibility. The Webmail authentication page is also used as a model for stealing bank details.
Google and Cloudflare remain at the top of the ranking of phishing hosts with Microsoft climbing higher owing to the online Excel app being used to display a phishing page as shown above. A clarification regarding the use of Cloudflare by malicious actors: Cloudflare is a CDN (Content Delivery Network). Web content is delivered through this network when a request is made to a website. This technique allows malicious actors to hide the true IP address of the host's server, making it more difficult to identify the actual host and thus lengthening the time it takes to remove malicious content.
- Google LLC (=)
- CloudFlare Inc. (=)
- Microsoft Corporation (+3)
- Dedibox Customer IP Range (New)
- Amazon Technologies Inc. (New)
- Namecheap Inc. (=)
- DigitalOcean LLC (-3)
- OVH SAS (New)
- Bitly Inc (-6)
- Domain Names Registrar Reg.ru Ltd (New)a
The POST CyberForce CSIRT is closely monitoring the phishing threat and will keep you informed in the next cybersecurity weather forecasts.
Vishing/Spam calls
There may have been fewer fraudulent calls this quarter, but there were still dozens. Our opponents are using the same techniques as last quarter, posing as Microsoft technical support. The calls are from spoofed numbers from the UK, Germany and Switzerland. However, the period brought a new development in the form of a police campaign in early September. Like Microsoft support spoofs, these calls are fraudulent in nature and extra vigilance is needed to avoid falling for them.
Malicious code
We have seen the emergence of a new family of malware called “SQUIRRELWAFFLE”, designed to target a very specific group of victims.
This malware is used in the first instance as a delivery system for other malicious activities. In particular, it is used to transmit the “Qakbot” banking Trojan horse and the Cobalt Strike tool used by ethical hackers for technical audits. It takes the form of a compressed .zip file that can be downloaded via a link in an e-mail. If the victim clicks on the link, the Microsoft Excel file opens and a code is executed downloading a new executable through which a C2 (Remote Command and Control) protocol is used by the malicious actors to take control of the victim's machine.
This is very recent malware, so the POST CyberForce CSIRT is monitoring its development and we will keep you posted in our upcoming bulletins.
“Flubot” malware was also in use over the period. Flubot is a malware program that spreads as a link in text messages sent from numbers that are spoofed and changed at random each time. Apart from one instance involving a text message received on Luxembourg numbers, it turns out that this malware is propagated from foreign lines (in the cases studied, these were French lines) via phones with two SIM cards. As the text messages containing Flubot download links were received on French lines, victims who also had a Luxembourg number and generated data traffic on the Luxembourg network allowed Flubot to use this traffic for its activities.
DDoS
We have seen a drop in DDoS attacks over recent months. The main techniques used are:
- ACK flood
- Unusual UDPs
During the period, we observed a peak of 2.9 Gbps for volumetric attacks. Customers with our anti-DDoS services benefit from protection against these types of attack.
Vulnerabilities
During the period, the following vulnerabilities were observed to be open to the possibility of abuse:
- CVE-2021-1675 - Windows Print Spooler or PrintNightmare
- CVE-2021-22005 - vCenter
- CVE-2021-38647 - Azure Linux
If you suspect that one of your vulnerabilities may have been exploited, it is always a good idea to have an expert check whether or not this occurred. The POST CyberForce CSIRT would gladly carry out these checks for you.
CVE-2021-1675 – Windows Print Spooler Remote Code Execution Vulnerability
When the Windows print spooler performs privileged operations incorrectly on files, it can be used to grant SYSTEM administrator rights allowing malicious actors to gain full control over a machine. This vulnerability, also known as PrintNightmare, allows malicious actors to execute arbitrary code through privilege escalation.
vCenter CVE-2021-22005
vCenter servers contain a vulnerability that allows a shell session to be opened on the remote server via arbitrary file upload to the Analytics service.
A malicious actor with network access to vCenter Server port 443 can exploit this issue to execute code on vCenter Server by uploading a specially designed file.
Azure Linux CVE-2021-38647
Azure Linux virtual machines had a flaw in the Open Management Infrastructure (OMI) agent. Users were not informed that this agent was being installed when deploying a Linux virtual machine. There was no update management system on Azure. Exploiting this vulnerability involved sending a request without an authentication header to one of the OMI agent's listening ports. In return, the attacker was given superuser rights to the machine.
An attacker could send a specially designed message over HTTPS to the port listening to OMI on a vulnerable system.
Have you had a security incident? Or do you think you might have been attacked via a vulnerable system within your company? The POST CyberForce CSIRT can help you resolve these incidents and answer any questions you may have about the cyber threat.

Written by
PitContact us
Do you have any questions about an article? Do you need help solving your IT issues?
Contact an expert







Our experts answer your questions
Do you have any questions about an article? Do you need help solving your IT issues?
